Most employees know to be careful when clicking on emails they receive from unfamiliar senders. But as cybercriminals and their tactics become more sophisticated, recognizing a scam has grown more challenging while the threats and consequences of these tactics have grown exponentially.
What Are Cybersecurity Threats?
The main cybersecurity threats are phishing scams, social engineering scams, malware, password theft and texting scams. Each tactic poses a threat to businesses through the potential loss of privacy, data, access to tools and even the loss of funds.
Just how big are the threats? Consider this: According to a recent report by insurance carrier Hiscox, in 2019, the average cost of a single cyberattack on a business reached just under $200,000. And big businesses are not the only ones affected. In fact, 43% of today’s online attacks are aimed at small businesses and less than 15% of these businesses are adequately prepared to address the threat.
How Cybersecurity Affects Businesses
Cybersecurity affects every aspect of a business’s digital presence, including websites, email, Point of Sale systems, customer data, human resources, accounts receivable and payable and even some offline operations. Essentially, cybersecurity should be a concern for almost every business operating today.
While taking technological steps to defend a business’s computer systems against cyberattacks is highly recommended, workforce awareness can also go a long way toward preventing digital disasters. Some small businesses are able to maintain proper cybersecurity defenses internally while others might require an external IT service to properly defend against attacks. No matter which route a business chooses, every business should train its employees to recognize threats and follow proper cybersecurity protocols.
To help ensure that businesses stay a step ahead of online fraudsters, employees should be on the lookout for these five common cybersecurity threats:
Phishing and Other Fake Emails
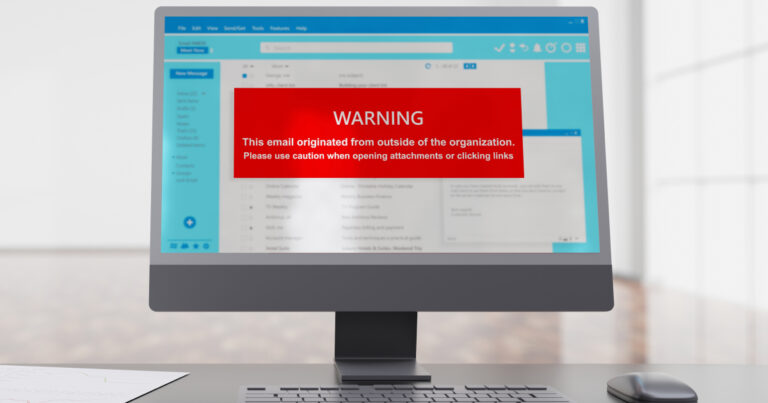
Phishing emails attempt to trick users into providing sensitive information, such as passwords or credit card information. They also try to get users to download dangerous malware by impersonating acquaintances or legitimate companies with whom the recipient might do business.
Signs that an email is a phishing attempt include poor spelling and/or grammar, a false sense of urgency, a request that the recipient provide sensitive information via an email or an online form, linked words or images that do not go to the destination they are supposed to, links to non-secure sites, and the inclusion of small bits of personal information that scammers could have obtained elsewhere online.
To protect against phishing and fake emails, workers should:
- Read emails carefully for spelling and grammatical errors and verify the sender before providing any sensitive information, downloading suspicious files or clicking on suspicious links.
- Be wary of any emails asking for personal or payment information. If workers are asked to provide sensitive information, they should call the business or go directly to its website to log in rather than clicking through on a link embedded in an email (most legitimate businesses will not ask for this information via email).
- Double-check the destination of any embedded links in an email before clicking through on them (when a user hovers over a link with his or her cursor, most email browsers have a feature that displays the web address to which the link directs).
- Avoid downloading or opening attachments in suspicious emails.
Social-Engineering Scams
Often employed in phishing emails, social-engineering scams aim to fool the recipient into thinking the sender is a trusted person or business. Common themes in this scam include the sender claiming to be a friend or family member in trouble and in need of financial help, pretending to be a trusted company threatening to limit or shut down a user’s service if requested information is not provided, offering a deal that seems too good to be true or claiming to be a collection agency of some sort seeking owed funds. In addition to generally being skeptical of such requests, users should employ the same precautions for dealing with phishing emails as described above to avoid becoming a victim of social engineering.
Malware
Malware is harmful software designed to damage or gain access to a user’s computer and its data. It is most commonly proliferated via phishing and fake emails but can be encountered when browsing the web or downloading files from FTP servers. Once the malware is activated, users may notice its presence based on slower computer performance, new and unrecognized toolbar icons in the browser or operating system, or more pop-up ads than usual. These are only symptoms of the more nefarious actions of the software now running in the background, which will attempt to access users’ accounts and ultimately steal money and data.
To protect against malware, users can employ tactics such as:
- Installing and maintaining regular updates of anti-virus and anti-malware software.
- Exercising extreme care when downloading free software or using peer-to-peer file-sharing applications, which are common sources of malware.
- Regularly backing up important files to the cloud or to a separate external storage device so they can be easily retrieved if a malware attack does strike.
- Ensuring emails come from a trusted source and even double-checking with the purported sender before downloading or opening any unexpected or suspicious files or attachments.
Password Theft
Password theft happens when a third party guesses or steals a user’s password or tricks the user into revealing his or her password. This type of cybersecurity theft can be especially detrimental to businesses that handle sensitive data or digitally retain the personal information of their customers. As passwords are often stolen via phishing or social-engineering attacks, following the precautions mentioned above for each of those threats can help prevent it. Further, employing hard-to-crack passwords and two-factor authentication for accounts containing particularly sensitive information can help minimize exposure to password theft.
Texting Scams
As the use of company-issued smartphones has grown, so has the threat of texting scams. One common type of texting scam known as “SMiShing” (pronounced like “phishing” with an “sm” on the front end) employs some of the same tactics as phishing, only via text message. These fraud attempts will often include links directing the recipient to a fake website that appears to look like the website of a legitimate company. Once users arrive on the fake site, the scammers will attempt to get the user to disclose sensitive or financial details.
To avoid falling victim to texting scams, one should:
- Avoid opening text messages from unknown senders.
- Refrain from sending any personal information to unknown senders via text.
- Avoid clicking on suspicious links sent via text. Go directly to a company’s website to log in.
- Avoid calling any phone numbers provided in suspicious texts or texts from unknown senders.
Note: While not always scams, spam texts are messages that are sent without the recipient’s request or permission often contain unsolicited advertisements. It is best not to reply to these texts as doing so confirms the recipient is an active user, giving the sender reason to continue spamming that number.
Businesses looking to protect their digital assets do not have to go it alone. When you need local, professional cybersecurity assistance, help is nearby and easy to reach. FTC IT Solutions offers a range of cybersecurity-focused services, including Managed Firewall Services, 24×7 Monitoring & Alert Response, Maintenance Updates Support, and Hosted Antivirus & Spyware. Visit the FTC IT Solutions website today to learn more and to step up your business’s online security.