As businesses rely more on internet-connected devices, the risk of cyberattacks increases. But a company can build a robust defense to prevent them by adequately educating employees on cybersafety, enforcing the use of strong passwords, and securing network infrastructure.
What Are the Most Common Cyberattacks on Small Businesses?
Small businesses face various types of cyberattacks such as phishing and other fake emails, malware, social engineering, password theft and texting scams. Small companies are often more vulnerable to cyberattacks because they employ weaker security measures, making an attack more lucrative for hackers. No matter the business size, owners and managers can take simple steps to increase security, significantly reducing the chances a hacking or cyberattack is successful.
How To Make a Business Cyber Secure
- Provide Employee Education: Ignorance is one of the greatest threats to cyber security. While a network can be secure, each employee who can log in to the Wi-Fi, check their email, or connect to a Point of Sale system, creates another potential access point for attackers. Regular cybersecurity training for employees can significantly reduce the chances of a successful cyberattack. Training should include lessons about phishing emails, social engineering techniques, password security, and keeping software current.
- Enforce Strong Password Policies: By enforcing the use of strong passwords throughout the organization, a company can block the most vulnerable access point to its data. Passwords should be complex, unique for each account and updated regularly. Businesses should also implement two-factor authentication (2FA) to add an extra layer of security.
- Secure Network Infrastructure: Businesses should ensure their network is properly secured. Firewalls, intrusion detection systems, and regularly updated antivirus software are all components of a properly secured network. Many small and medium-sized businesses need more resources to secure their network infrastructure, and they will find a managed firewall service and hosted antivirus software helpful and cost-effective.
- Complete Regular Software Updates: Keep all software, operating systems, and applications current. Software vendors often release updates to fix vulnerabilities that cyberattackers could exploit, and an out-of-date system leaves a business open to older forms of attack. Companies should enable automatic updates whenever possible and regularly patch and update all systems.
- Institute Access Control and Privileges: Not every user needs access to all company networks and software levels. Businesses should limit user access to systems and data based on job requirements by assigning user privileges on a need-to-know basis to minimize the risk of unauthorized access or accidental exposure of sensitive information.
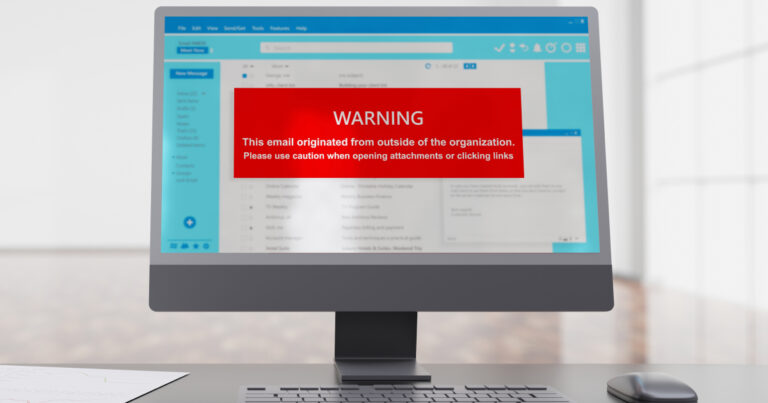
- Implement Secure Email Practices: While employees should be trained to recognize email threats, businesses can further secure email vulnerabilities by deploying email filtering and spam detection mechanisms to prevent phishing attacks.
- Schedule Regular Security Assessments: Conduct periodic security assessments and penetration testing to identify vulnerabilities throughout the network. Like they would for any other aspect of the business, owners and managers should regularly review and update security policies, procedures, and incident response plans based on the findings.
- Stay Informed: Cyberattacks are a constant threat to businesses and like any threat, they necessitate educating business owners about the changing landscape. Business owners and managers should make it part of their job to stay updated on the latest cybersecurity threats, trends, and best practices. To avoid emerging threats, they should monitor reputable sources such as cybersecurity blogs, industry publications, and relevant security organizations’ alerts.
How To Minimize the Impact of Cyberattacks on Businesses
Despite robust preparation, businesses can still fall victim to a cyberattack. Knowing that no one is perfect, business owners should plan for the worst and protect their assets by setting up data backup and recovery systems and creating and maintaining an incident response plan.
- Set Up Data Backup and Recovery: Cyberattackers will often destroy or hold data hostage, but when a business backs up its data on a secured server and then quickly recovers it, the attacker has no leverage. Companies should implement a strategy to back up critical data frequently to secure, off-site locations or on a cloud-based service. This practice ensures businesses can recover their data even if it becomes compromised or inaccessible.
- Create an Incident Response Plan: By developing a comprehensive incident response plan to address potential cyberattacks, businesses can prepare to move on from the worst situations. This plan should include steps for identifying, containing, eradicating, and recovering from a security incident, and it should be regularly tested and updated to ensure its effectiveness.
A successful cyberattack can be devastating to a business. Along with direct monetary losses, data could be held hostage or even lost entirely, and attacks can even spread to customers or other businesses. Companies should act now to secure their networks, train their employees, and set up data backup and recovery systems so they are ready for the next attempted cyberattack.
Do you want to protect your network but lack the in-house resources to secure your business against cyberattacks properly? Visit ftc.net/business today to learn more about our managed firewall and hosted antivirus software, plus our complete list of IT Solutions for businesses of all sizes.